Over the last week, as New Zealanders begin to change their jandals (flip-flops / thongs) for shoes, I’ve noted a significant increase in the number of “warnings” being posted in my social network feeds. This is not uncommon and it’s not unique only to my network of contacts as these articles point out.
 Now, for the most part, folks in my social stream tend to only get caught on an infrequent basis by these messages. I do my best to flick a link back if it’s an obvious hoax, as do others who we share as common contacts. I have been caught myself and have more than once shared something which, if I’d relied on more than wishful thinking, would/should have been filtered out.
Now, for the most part, folks in my social stream tend to only get caught on an infrequent basis by these messages. I do my best to flick a link back if it’s an obvious hoax, as do others who we share as common contacts. I have been caught myself and have more than once shared something which, if I’d relied on more than wishful thinking, would/should have been filtered out.
So – why do these attacks work, why do the hoaxes perpetuate, and what can we do as a community to reduce our chances of passing on misinformation to our networks?
The simple answer is diligence.
Part 1 – Why they work…
Normalisation and Demand
As social sharing becomes more and more normalised, consumers are demanding access to their life-streams from more locations and on more devices. This demand is more than catered for by an army of develops building applications which leverage the APIs (the way a service can be interacted with programmatically) that the social platforms are publishing. The issues with this are:
- Anyone can write an application: They can make it available for a mobile platform, as a browser plugin, as an ‘app’ on the platform itself. This however does not mean the application is:
- Maintained against the current set of API / service functionality
- Well designed / secure
- Doing *just* what it says it will
- User Interface (UI)/ User Experience (Ux): Not all of these platforms are easy to interact with, many of them target devices used for ‘slack time’ focus and as such, often, neither the interface nor the environment allows for the interactivity required to make well-informed decisions as to pass on the information or not.
- Openness does not necessarily translate to trustworthiness: The openness of the social environment drives innovation, the openness also allows for the exploitation of folks who may not (care for) investigate(ing) the function they are allowing to access their information.
Human Nature
These scams also prey on basic human nature, be it greed, egocentricity, natural philanthropy etc etc (there is an unfortunately long list of traits which contribute).
- The fear of missing out (FOMO): NOT being part of the ‘next big thing’, not having the bragging rights of “Oh yeah, I was on that when it first launched” can be a big influencer when people decide to create an account, or link their existing information to a new service.
- People trust their friends: (Even when they aren’t friends). A message appearing in your timeline notifying you of something you feel others should know has more credibility through familiarity (because you’ve read their updates for a while, and they’re often interesting/funny/legitimate, than if you were to read a similar story in a less interactive environment (such as reading the information in an offline context where more steps are required to pass on the data).
- Accounts are Insecure: Couple the above reasons with the relative insecurity of the credentials the average person uses to ‘protect’ their account – and you’ve got an efficient and believable angle through which to launch your attack.
- Accounts can be fake: Minor misspellings, the use of additional and/or cyrillic characters in a name are all effective, and often a change which doesn’t register in the consciousness of a time-poor glance at an update stream.
- The machine knows who you are: Based on what information is already ‘out there’ in terms of your digital footprint, there are many tools which can assist a social engineer to discover likely contacts they could impersonate in the hopes of having you accept them as a legitimate contact and thus gain access to your ‘inner circle’ of (online) trust. Even the social platforms themselves are getting in on this action, more to strengthen ties between subscribers and increase their own stickiness than to scam their users, but – as with most tools, the usage of the functionality is the differentiating factor in terms of legitimate, and malicious use.
- Impersonation is Effective: If it says it’s secure – it must be legit, right? … yeah, ahh.. no. Malicious folk will also leverage current (or fake) events to entice the unwary into clicking something that, while it uses the same colour scheme, fonts and layout – is not legitimate.
People are become more aware of privacy
Given the above points, and the increasing number of exploits, people are starting to take more notice of what they are doing and what they allow to happen to their data. People genuinely WANT to help their contacts, and often this results in a ‘click first, to warn everyone… THEN read the article’ approach to information dissemination. Unfortunately, sometimes corrections can come too late and the damage has already been done – therefore we have a moral responsibility to others in our networks to minimise our mistakes wherever possible.
- Privacy reaches further than your own information: This is not only a problem for the person MAKING the choice over the application, but it becomes a problem for those who they connect to. Privacy has been proxied to your social network contacts and thus, what THEY do affects YOU.
- Information flows faster than our fingers: Given our increasing connectedness, even if closer inspection reveals the information to be misleading / a hoax / malicious, the damage has been done. Others have seen and passed on the link / information to THEIR networks and, even if you delete the message from your feed, the great copying machine that we know as the Internet has done what it does best and disseminated the data… rinse, and repeat onward through the network.
Part 2- Why they perpetuate…
Because people have poor memories, we don’t NEED to remember details, we only need to recall just enough to formulate a search query, the information will then be delivered to our screens.
Factor in the ever growing numbers of technology adopters, and you have a whole next generation of folk who might fall for the same scam as last time. SPAM (of which it could be argues this is a form of) works in much the same way… Target a large enough population and you are bound to find sufficient distracted/non-pessimistic or naive/gullible respondents to make the communication worthwhile.
As discussed in Part 1, people WANT to help others – if they are distracted, having an optimistic day and or are simply naive, they will pass the message on.
Part 3 – What we can do…
Everyone has their bad days, but as a community – it is our responsibility to point out instances of these scam messages so the originators can contact their community to let them know they fell for one and that knowledge itself can then percolate through, hopefully avoiding repeats in the future – at least giving pause (and a location for future scam checking) for folks before the next scam starts doing the rounds.
Resources that I personally use to check out dodgy sounding stories are:
- FaceCrooks – They are also on Facebook, and well worth the ‘like’ as they update frequently with the current scams doing the rounds so you can be forewarned
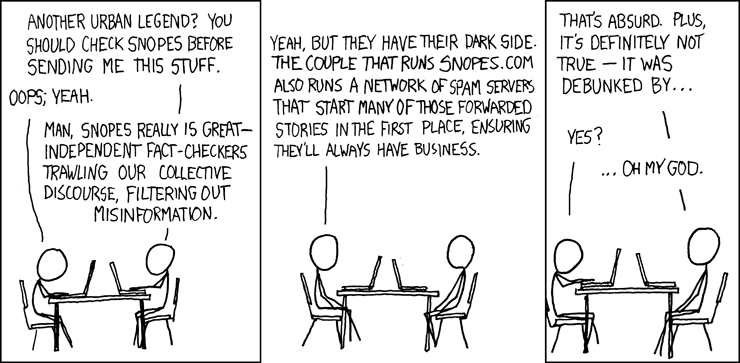
- Snopes – “The definitive Internet reference source for urban legends, folklore, myths, rumors, and misinformation.”
- Scambusters
Such is the widespread nature of scams that governments are also funding information sites such as the New Zealand Governments Department of Internal Affairs who post the latest reported scams here